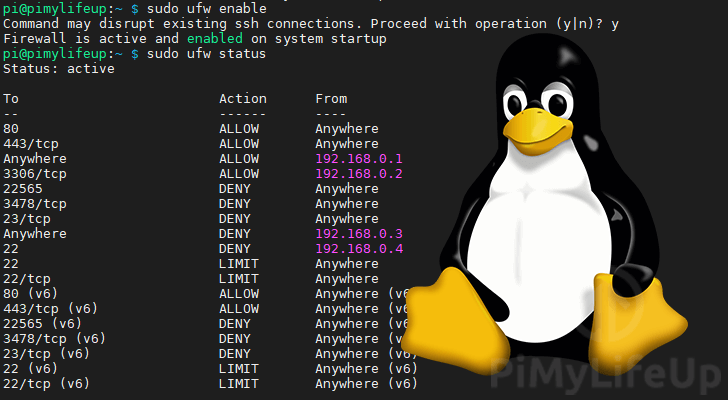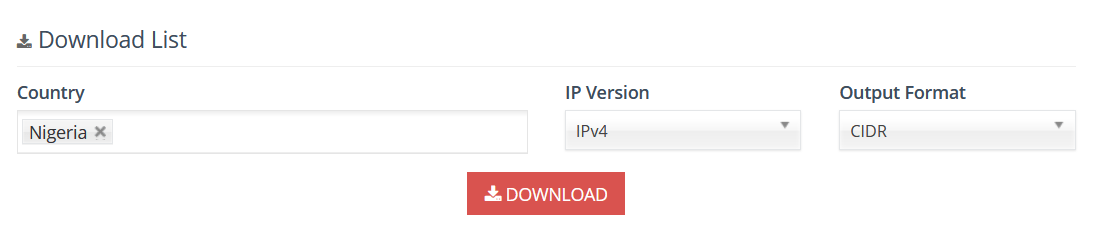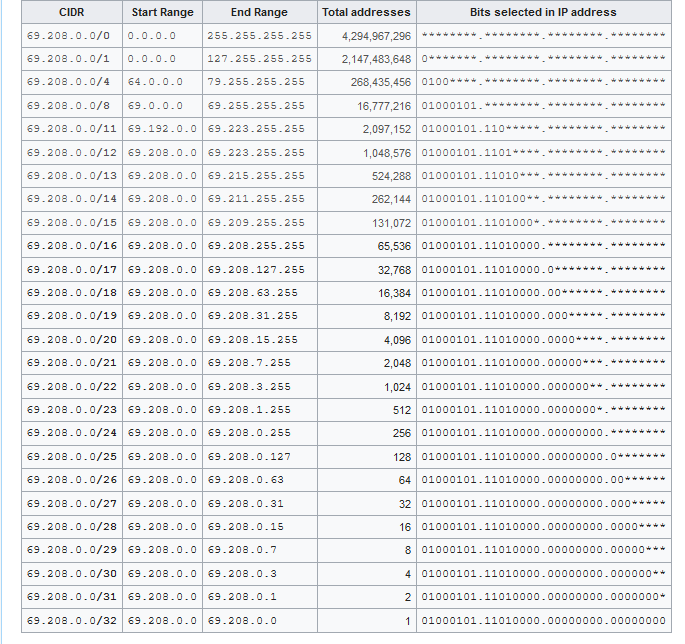
pg2ipset and ipset-update - Quickly and Easily block IP ranges on the bluetack lists, countries, custom lists, and tor exit nodes using the ipset kernel module and iptables : r/linux

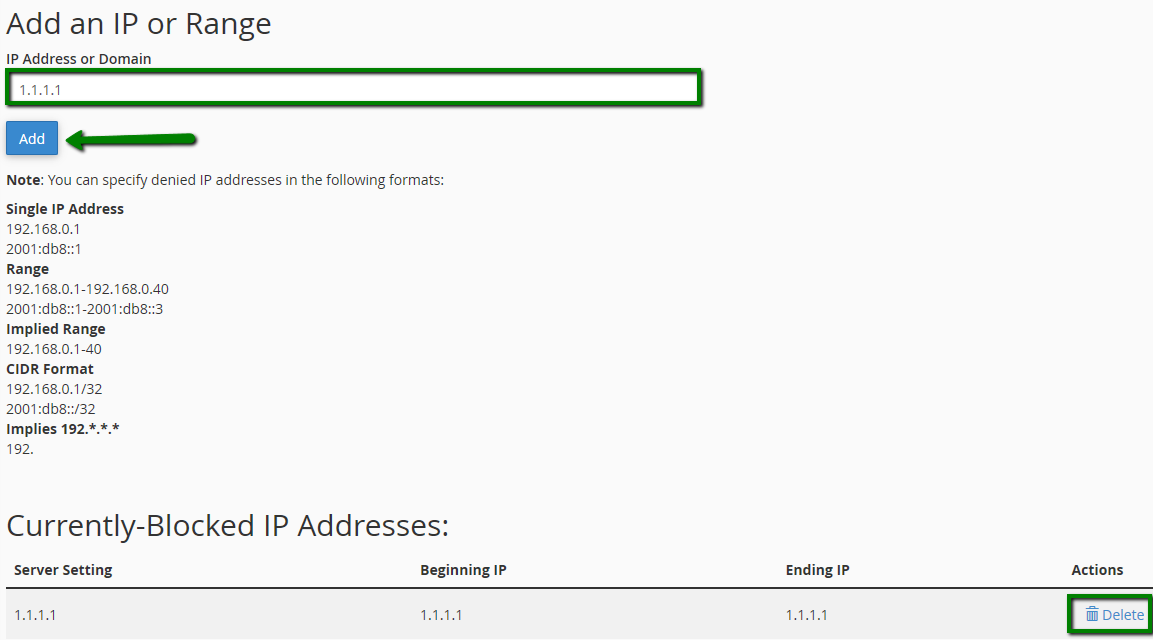
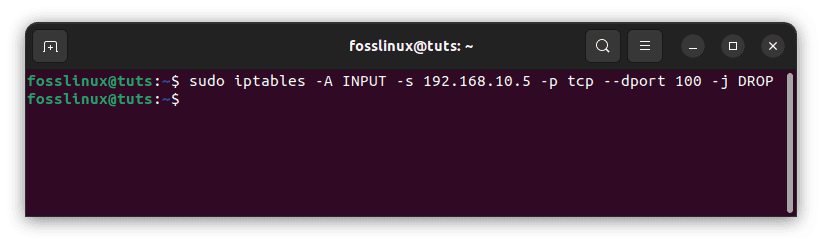
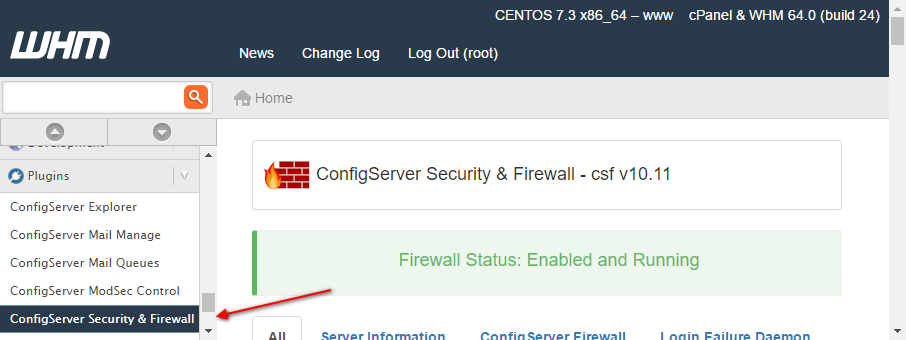
How to whitelist/blacklist IP addresses using command line and GUI in CSF firewall? - Knowledgebase - AccuWebHosting
![Blocking an IP in Linux Firewall [Iptables, UFW, Firewalld] Blocking an IP in Linux Firewall [Iptables, UFW, Firewalld]](https://operavps.com/wp-content/uploads/2023/09/Blocking-an-IP-in-Linux-Firewall.jpg)